Mystery Around Venezuelan Cyberattack Deepens, with New Discovery of "Highly Destructive" Wiper

The mystery around a cyberattack that struck Venezuela's state-owned oil company in December is growing, following an announcement by researchers this week that they had discovered a "highly destructive" wiper program that appears to have been designed to target the oil company and may have been used in the December attack against it.
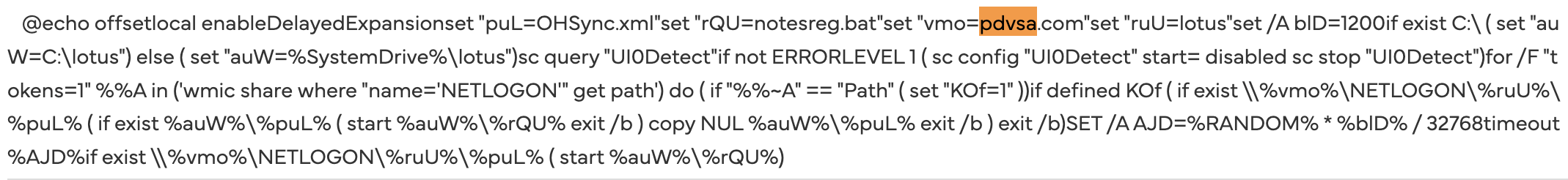
Months before that cyberattack, and before US forces invaded Venezuela to seize then-Venezuelan President Nicolás Maduro, someone compiled the destructive wiper files and hard-coded the domain of Venezuela's state-owned oil company – Petróleos de Venezuela, or PDVSA – into a script used to trigger the wiping operations. The latter was aimed at erasing data and critical files from targeted systems, to render them inoperable. The hard-coded domain ensured that if the malware infected systems on any network outside of the PDVSA domain, it would not wipe their files.
This week researchers at the Russia-based security firm Kaspersky Lab announced discovery of the code, which they dubbed Lotus Wiper. The company did not say that it targeted PDVSA, only that it had targeted the "energy and utility" sector in Venezuela in December and January. But Ben Read, a security researcher and nonresident fellow at the Atlantic Council's Cyber Statecraft Initiative, noticed that PDVSA.com was hardcoded into one of the wiper's files posted online, indicating that this version, at least, was a precision weapon configured to target the oil company.
Oleg Shakirov, a PhD student at Johns Hopkins University's School of Advanced International Studies, noted in a blog post that the hardcoded PDVSA.com domain shows that the attackers wanted to avoid damage to non-targeted systems if the wiper infected them.
"This essentially limited the wiping operation to the specified network domain," he writes. "In case the same batch script was launched on a computer outside of the domain, it would never trigger the next phase."
He acknowledges, however, that the wiper could potentially be repurposed and launched against different targets, if the attackers changed the domain name hardcoded in the script – as long as there is nothing else in the code to limit the attack to the oil company.
December Attack
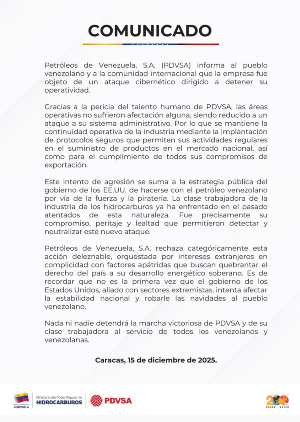
Last December 15th, PVSDA announced in a statement posted online that it had been hit by a cyberattack that had struck two days earlier on the morning of December 13, a Saturday.
Although reports at the time indicated that the cyberattack was caused by ransomware, the discovery of the Lotus Wiper raises the possibility that it might have been a wiper instead. But if Lotus was the malware used in that attack, Kaspersky researchers note that it did not have a ransom demand coded into it, and its purpose was strictly destructive.
“We believe that this wiper is extremely targeted, has no financial motivation, and aims to erase all of a device’s files and data,” the researchers wrote in their report.
The attack occurred as significant tension was building between the US and Venezuela, after the US began amassing military ships in the region, and President Donald Trump announced that he had authorized the Central Intelligence Agency to conduct covert operations in Venezuela. The Trump administration claimed the activities were aimed at thwarting illegal migration from the country and the shipment of illegal drugs to the US. But one week before the cyberattack occurred, the US seized a sanctioned oil tanker that had been carrying Venezuelan crude oil sold by PDVSA.
When the cyberattack subsequently occurred, the oil company and oil ministry blamed the US for it, pointing to Trump's longstanding desire to de-stabilize the country in order to oust Maduro. Two weeks later, on January 3, US military troops invaded Venezuela and seized Maduro – after which President Trump announced the US would be "running" the country in his place.
How to Contact Me
If you have information about the cyberattack on the PVSDA, or wish to speak with me about anything else (excluding marketing pitches), you can contact me securely, using a non-work device or email address, via the following:
Signal - KimZ.42
Keybase - kimzet
kzetter@protonmail.com
If you'd like to advertise on Zero Day, you can reach me at countdowntozeroday@gmail.com.
It's not clear if the US was behind the December cyberattack, but there is precedent for US cyber attacks in Venezuela during Trump's first presidential term.
A Wired story revealed last year that in 2019, the CIA had hacked Venezuela's state-administered payroll system used to pay its military. The goal was to anger members of the military so they would blame the Maduro regime for incompetence and shift support to his political rival. And CNN also reported that around the same time, the CIA had launched a cyberattack that disabled the computer network of Venezuela's intelligence service, and US Cyber Command had launched a cyberattack aimed at disrupting the satellite communications of the Wagner Group, the Russian mercenary group that reportedly had a presence in Venezuela at the time.
What's more, Trump and a military official seemed to imply in statements made this year after the January raid, that the US had used a cyberattack against Venezuela's grid to black out parts of Caracas before the raid. News reports seemed to confirm this, though this has since been called into question, and no evidence of a digital attack against the Caracas grid has been discovered. That's not the case with the December attack, in which the oil company and government confirmed an attack had occurred.
Wiper Squared
The Lotus malware discovered by Kaspersky researchers is designed to be very thorough in its destruction of data and files. It overwrites data on hard drives, deletes backups and erases system files to render machines inoperable and unrecoverable. It also wipes system logs and update journals to eliminate evidence of its activity on infected systems.
Notably, before it executes the wiping operation, the malware moves to suppress the operation of the Windows Interactive Services Detection service. The latter issues alerts to users if something attempts to run on their computer in the background. But Microsoft eliminated this from versions of its operating system after Windows 10, version 1803, suggesting the attackers knew that systems they were targeting in Venezuela were using old legacy software. Venezuela has had a problem keeping computer systems current, due to sanctions that prevent US tech companies from licensing their software to it. The Kaspersky researchers say the focus on the Windows Detection service suggests the attackers may have compromised the oil company's domain "long before the attack occurred" to gain knowledge about the Windows software they were using.
According to a compilation timestamp in the files, the wiper code was compiled in late September 2025, meaning this is when the developers ran the source code through a compiler to turn it into binary. Compilation timestamps can be altered by coders, however, to make it appear that code was compiled at a different day and time than it actually was compiled.
"Assuming the compilation time of the PE file has not been altered," Kaspersky writes in its report," this indicates that the attacker had been preparing for this attack for several months.”
If you find this article valuable, you can leave a one-time tip to express appreciation to the author.
Lotus and the December Attack
There is currently no proof that the Lotus Wiper was the malware used in the December incident, but the company's domain name in the attack code and the timing of the attack suggest a connection.
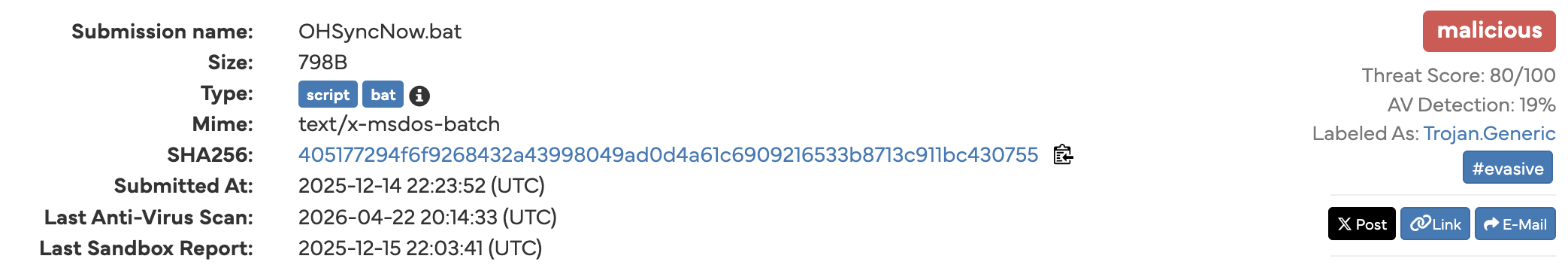
The day after the December cyberattack occurred, someone uploaded the Lotus Wiper files to a web site called VirusTotal, from a machine in Venezuela. VirusTotal is a malware repository and scanning service used by network security teams and researchers to determine if malicious files they find on systems are malicious. Researchers upload suspicious files to the site, where dozens of different antivirus engines scan them to determine if they are malicious.
Kaspersky didn't indicate that the Lotus Wiper files were uploaded to VirusTotal – it said only that they were uploaded to a malware repository – but a search of VirusTotal shows that the wiper files were uploaded to the site on December 14; shortly after, at least one of the files was uploaded by someone to a second site called Hybrid Analysis.
A day later, PVSDA released its statement acknowledging a cyberattack against its systems had occurred. The company played down the attack, however, denying that it had impacted operations in any way. It said that the attack had only impacted some of the company's administrative systems.
"Thanks to PDVSA's human talent expertise, the operational areas were not affected at all," the company said in a statement.
Initial news reports indicated that the attack had been done with ransomware. But a PDVSA source told Reuters that any problems that occurred on its systems were due to the company trying to respond to the ransomware attack – specifically, the source said, antivirus software the company had used to address the attack had impacted administrative systems. But, sources asserted, oil output, refining and domestic distribution were not affected.
Other news reports painted a much different picture, however. They indicated that the attack had hit "key" administrative systems and, as a result, the company's oil export operations were disrupted. PDVSA reportedly told staff to shut down their computers, remove any external devices connected to them, and sever all internet connections, including WiFi and Starlink connections. As a result, systems used to manage import and export data at the country’s primary crude terminal were still offline the Monday after the attack, which delayed scheduled loadings of product.
And a month later, Bloomberg reported that Venezuela's oil industry had still not recovered from the cyberattack. The oil company still did not have working systems, and employees were running day-to-day operations on WhatsApp, Telegram, phone calls and handwritten notes. This had slowed salary payments to workers and payments to contractors.
"The company still cannot access system platforms on which accounting, payments and production data run," sources told the publication. "Internal email is also down [and] employees are also in the dark on payments." A PDVSA retiree said he couldn’t verify his pension deposit, because the company’s portal was down.
Bloomberg also wrote that the attack had not been limited to IT systems but had also impacted the SCADA system that runs processes in refineries, compression plants and pipelines.
Johns Hopkins' Shakirov says it's curious that the December attack – a confirmed attack with seemingly malware evidence – has received little media and public attention in comparison to the phantom grid attack in January that may have never occurred.
"Everyone talked about [the January grid attack] as some kind of new era of cyberwarfare, while in this case we have very tangible technical analysis, [yet little coverage]," he told Zero Day. "I don't have any takeaways from this; I just find it very curious."
See also:
Cyberattack Targeting Poland's Energy Grid Used a Wiper
UAE Recruiting US Personnel Displaced by DOGE to Work on Its Military AI
Booz Allen Tech Contractor Took IRS Job Specifically to Leak Trump Tax Records