Trenchant Exec Says He Had Depression, Money Troubles When He Decided to Sell Zero Days to Russian Buyer; Also, New Info Reveals Nature of His Work for Australian Intelligence Agency

Peter Joseph Williams, a former L3 Trenchant executive recently convicted of secretly selling zero-day exploits to a Russian broker, says he was suffering anxiety, burnout, years of depression, and financial difficulties when he decided to steal exploits from his US employer and sell them to the Russian buyer.
Williams, who was promoted to general manager of Trenchant during the three years he was stealing from his company, explained the circumstances around his fateful decision in a letter submitted to the DC District Court before his recent sentencing. His attorney also described his crime spree as "an unfortunate period of extraordinarily poor judgment exacerbated by severe job stress and exhaustion."
An Australian national who has lived in the US since July 2023 while working out of Trenchant's DC offices on a visa, Williams wrote that at the time he committed the offenses, he was "experiencing significant professional pressure and personal anxiety." But instead of seeking help or "removing" himself from circumstances he said he was not handling well, he signed contracts worth $4 million to sell eight of his company's hacking tools to a Russian company called Operation Zero – a firm known to sell exploits to the Russian government and other non-NATO countries.
Williams, who is 39 years old and the father of two young children, acknowledged that his depression and burnout were not the causes of his crimes, but offered the court details about his mental state as explanation for why his judgment was impaired at the time and why his actions deviated so far from a lifetime spent in service to the Australian government and military. Williams' wife and older brother wrote similar letters to the court about the strain he was under between 2022 and 2025 when he committed his crimes – Williams was the sole breadwinner for his family and handled all financial and administrative aspects of their lives, in addition to his stressful job, his wife wrote; and his criminal actions were completely out of character for someone who had devoted his life to protecting his country and its ideals.
Williams had served in the Royal Australian Air Force reserves and had also worked a number of years for the Australian Signals Directorate, an Australian intelligence agency equivalent to the US National Security Agency. His subsequent work for Trenchant in the private sector could also be seen as service to his country, since it involved selling hacking tools to the Australian government and allies for their use in breaching the networks of Russia and other adversaries to gain intelligence. But in selling some of the same tools to the Russian buyer – a buyer known to supply the Russian government – he potentially gave Russia tools that it could use to hack Australia, the US and other countries. Prosecutors say the tools Williams sold included "incredibly powerful" zero-day exploits that would have allowed Russia or any other buyer to "potentially access millions of computers and devices around the world, including in the United States."
For this, prosecutors sought a nine-year prison sentence for Williams; the judge gave him seven years and three months.
In arguing for a lesser sentence, Williams' attorney told the court that the exploits Williams sold weren't classified government tools but were instead "commercial products" that Trenchant had the ability to sell to any customer, without needing government permission. The Russian buyer-reseller also had commercial customers in addition to government ones, Williams' attorney noted, and prosecutors had no evidence his client "knew or intended" that the buyer would re-sell the products to the Russia government or to any other foreign government. If prosecutors believed he knew the exploits would go to Putin's regime, "this case would involve different, more serious, charges," he told the court.
Furthermore, although his client had had access to all of Trenchant's products, he only sold ones to the Russian buyer that he believed were "least likely to create harm."
Following, is new information about this extraordinary case – from court documents, property records, an Australian news article about Williams' prior work for the Australian intelligence community and other sources – that provides new insight into Williams, his financial circumstances at the time he committed his crimes and more.
How to Contact Me
If you have information about Peter Williams, Trenchant or his sale of exploits to Russia -- or information about similar activity by others -- you can contact me securely on Signal at KimZ.42 or via email to: kzetter@protonmail.com. Use a non-work device or email address to reach out.
If you'd like to advertise on Zero Day, you can reach me at countdowntozeroday@gmail.com.
Brazen Actions
The news of Williams' crimes stunned the security and intelligence communities when it became public in October. Although it's not the first time someone developing offensive hacking tools for NATO governments has also sold tools to buyers in non-NATO countries, this has generally involved independent security researchers selling their own work, and selling it to countries like Israel or the United Arab Emirates, with whom the US and allies have a cooperative relationship.
But there are many aspects of Williams' case that have been new and shocking to these communities: the fact that he was a top executive stealing and selling tools from his employer; the fact that he sold them to a Russian buyer that might provide them to the Russian government to hack Ukraine, Australia and other western targets; and the fact that Williams had previously worked for an Australian intelligence agency to help defend government and military networks from hackers and had now betrayed his former colleagues by undermining their work.
But what was most astonishing was the brazen recklessness with which Williams committed his crimes. In October 2024 after Trenchant learned from the FBI that some of its hacking tools had fallen into the hands of a foreign zero-day broker, the company launched an internal investigation to determine how the code might have been stolen or leaked from its servers. Williams, who had recently been promoted to general manager of the company, was given direct oversight of the investigation, which resulted in a subordinate of Williams being fired. Prosecutors say he stood idly by as the worker was blamed for Williams' own conduct. He also continued to sell to the Russian buyer even after discovering that a different broker in South Korea was re-selling some of the same code Williams had sold to the Russian buyer – suggesting the code was likely being sold and re-sold to a wide swath of buyers, including, potentially, criminal groups.
But perhaps Williams' most brazen act was continuing to steal and sell Trenchant exploits to his Russian buyer even after he knew the FBI was investigating the theft, and even while Williams was meeting with federal agents to discuss their investigation. He also made ostentatious purchases – with money tied to the sale of the exploits – during the FBI's investigation. For example, just days before he met with federal agents to discuss their investigation, Williams finalized the purchase of a $1.5 million home in DC with a $300,000 cash down payment. He was later forced to forfeit the home as part of his spoils when he pleaded guilty just four months later.


Australian Signals Directorate Work
Williams grew up in a lower middle-class household in Australia, according to his attorney, and from a young age exhibited a strong aptitude for mathematics and computer programming. He got an unspecified degree from the University of Sydney, and served at some point as a reservist in the Royal Australian Air Force until his professional demands made this impractical. It's not clear if he ever served active duty in the military – Australia has no conscription, and you can join the RAAF reserves without having ever served active duty. Williams' brother told the court he suffered an injury "during his service in the Australian Defence Force" and had chronic back pain as a result. Williams wore a back brace and took strong pain medication to cope, according to his brother.
After college, he began working for Australia's Defence Signals Directorate – which was known as DSD until 2013 when it became the Australian Signals Directorate, or ASD. The directorate, whose motto is "Reveal their secrets, Protect our own," has both an offensive and defensive remit, similar to the NSA in the US. It engages in foreign signals-intelligence collection and offensive cyber operations (both are forms of espionage), but also helps secure Australian military and intelligence networks.
Between 2008-2009, Williams worked in Canberra for the DSD's Evaluations and Industry Coordination section – a team ostensibly involved in cyber defense. His wife, whom he met in 2007, worked for the same division.
Williams' wife is not identified in court documents, but Australian news media have identified her as Su-en Williams, formerly Su-en Yek, a name that also appears on property records for the house the two bought in Washington, DC. Su-En earned a Ph.D from the School of Computer and Information Science at Edith Cowan University in Perth and has a handful of research articles about information security that were published online in the Journal of Information Warfare in 2004 and 2005 when, it appears, she was still a doctoral candidate.
Though it's not clear where Williams and his wife met, it's likely they met on the job. She writes in her letter to the court that they met "early in our professional lives while working in national security related roles in Australia." Williams also notes in his letter to the court that since 2007, the year he met his wife, "the vast majority of my social circle has been from the intelligence or cyber security communities. I have kept very few connections from my past life because of the work constraints and commitments I had to make." The two married in or around 2012, and have since had two children together, who are now 11 and 6 years old.
In his job at the DSD, according to the Daily Telegraph, Williams helped vet and certify technologies used on or to protect Australia's classified military and intelligence networks. The technologies they evaluated would have included things like encryption devices and cryptographic systems, authentication systems, network firewalls, operating systems, and database software.
Williams' team had authority to tear open the systems and hunt for hidden flaws that adversaries could use to penetrate Australia's classified networks and steal secrets. Based on their analysis, approved technologies would then be added to the Evaluated Products List – a list of trusted technologies shared among members of the Five Eyes spying partnership (the US, UK, Canada, Australia and New Zealand). The evaluations were ostensibly done for defensive purposes, but presumably if Williams' team found vulnerabilities in systems that Australia knew were being used in the networks of adversaries, that information could have been shared with the DSD's offensive hacking teams to be used to exploit foreign systems for spying. This would have made Williams' subsequent move into the offensive side of vulnerability research at Trenchant a natural one.
If you find this article valuable, you can leave a one-time tip to express appreciation to the author.
The Birth of Trenchant
Around the time that Williams and his wife were working for the DSD, Trenchant was coming into being – or at least the companies from which it was eventually formed were coming into being.
Trenchant was formed in 2018 through the merging of two Australian firms – Azimuth Security and Linchpin Labs. Both were boutique firms that built solid reputations in government circles for uncovering vulnerabilities in mobile phone operating systems and other software programs and creating exploit code to hack them. Azimuth, founded in 2008 by titans in the vulnerability research field – Mark Dowd and John McDonald – famously created a tool that the FBI used in 2016 to unlock an iPhone belonging to Syed Rizwan Farook, who had been responsible for a terrorist attack in San Bernardino, California. Linchpin Labs was launched in 2007 by former Australian intelligence officers and specialist vulnerability researchers and exploit developers from Five Eyes intelligence agencies, who leveraged their expertise and intelligence community contacts to sell tools and services to the Australian government and its Five Eyes allies.
In July 2018, the New York-based defense contractor L3Harris Technologies acquired both companies and renamed the new entity L3 Trenchant, which continued the vulnerability-research and exploit-development work that Azimuth and Linchpin had started
It's not clear when Williams left the DSD, but prosecutors say in 2016 he began working for one of the companies that would later form L3 Trenchant. Prosecutors don't name the firm, but it's been reported by Risky Business that the company was Linchpin Labs. During the time he worked for Linchpin, Williams and his wife were reportedly living in Sydney’s affluent Bondi Junction neighborhood. His wife was reportedly still working for the government in 2017 as a cyber capability manager for Australia’s Department of Defence.
It was about four years into his work for Linchpin/Trenchant, Su-en Williams notes in her letter to the judge, that her husband began to change. During and after the COVID pandemic, she wrote, life stresses began to impact him. Williams himself told the court that he first began experiencing symptoms of depression and anxiety in early 2020 – the point at which the pandemic was beginning to spread around the world.
His workload increased substantially and, according to his wife, he had operational and financial responsibilities as well as the "emotional burden of supporting staff through periods of stress, restructuring, and uncertainty." Presumably the restructuring refers to the changes that occurred at Linchpin Labs after it was acquired by L3 Harris in 2018 and absorbed into the American company's culture and offices. At some point, Williams also became the family's sole provider financially.
His wife told the court that her husband ignored his growing signs of serious burnout and declining mental health as well as her suggestions that he step back from his responsibilities to re-prioritize. She says he refused because he felt a "deep obligation to those who depended on him." She didn't mention any financial strains in her letter to the court, but Williams' brother wrote that Williams told him that during the time he committed his crimes "he was under significant financial pressure and stress from his job."
His work required frequent travel to Canada, the US, UK and New Zealand, which took physical and emotional tolls on him, and his brother believed "the cumulative weight of his personal and professional responsibilities, combined with the financial pressure Peter felt as the sole income earner for his family" contributed to the circumstances in which he made his poor decision to start selling exploits.
But prosecutors say that between 2022 and 2025 when Williams committed his crimes, he earned "in excess of $2.25 million" from his job at Trenchant. In 2024 alone, the year he was promoted to general manager, he earned more than $775,000. They say that if Williams had money troubles, it was only due to the luxury lifestyle for which he was developing a taste, and a selfish need to keep that lifestyle afloat. He was "a person with significant education and resources, the head of a large company, an individual with a highly paid and coveted job, with lucrative assets," they say, who had a growing "desire for more money, a better lifestyle, bigger home and more jewels."
The contracts he signed with the Russian buyer would have earned him at least $4 million over time as the terms of those contracts played out. Prosecutors say he only collected about $1.3 million of this, on top of the more than $2.25 million he earned in salary and other benefits from Trenchant during the same time period.
During this time, they note, he spent about $1.3 million on "indulgent items" that included: luxury cars (a 2022 Tesla Model X and a 2018 Porsche Panamera), more than $718,000 on personal and family vacations, diamond and gold jewelry worth more than $12,500, four pieces of luggage costing more than $5,000, and a $300,000 down payment on a newly renovated $1.5 million home in DC.
His attorney says that Williams' spending was intended to compensate his wife and children for his increasing time spent away from them due to his demanding job.
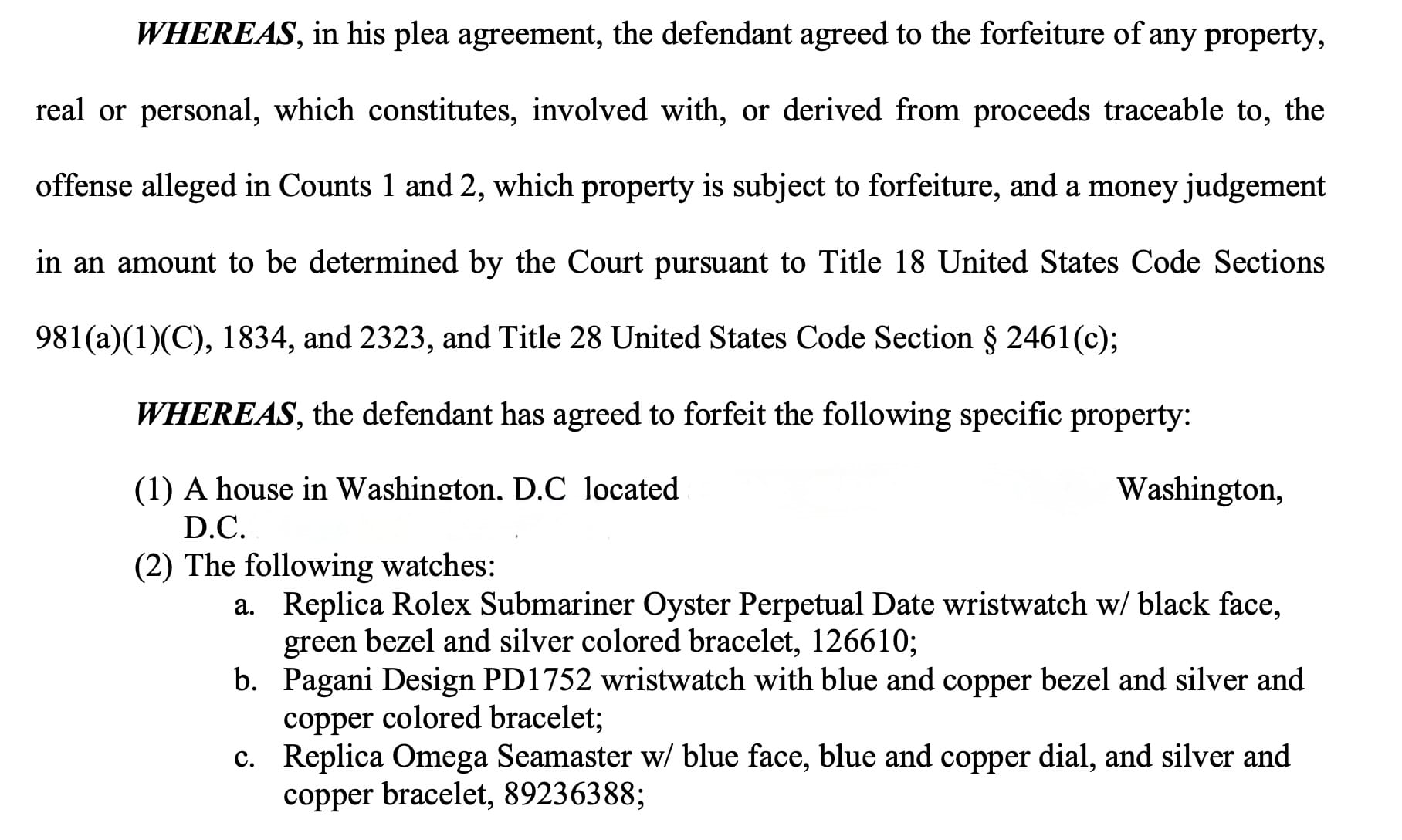
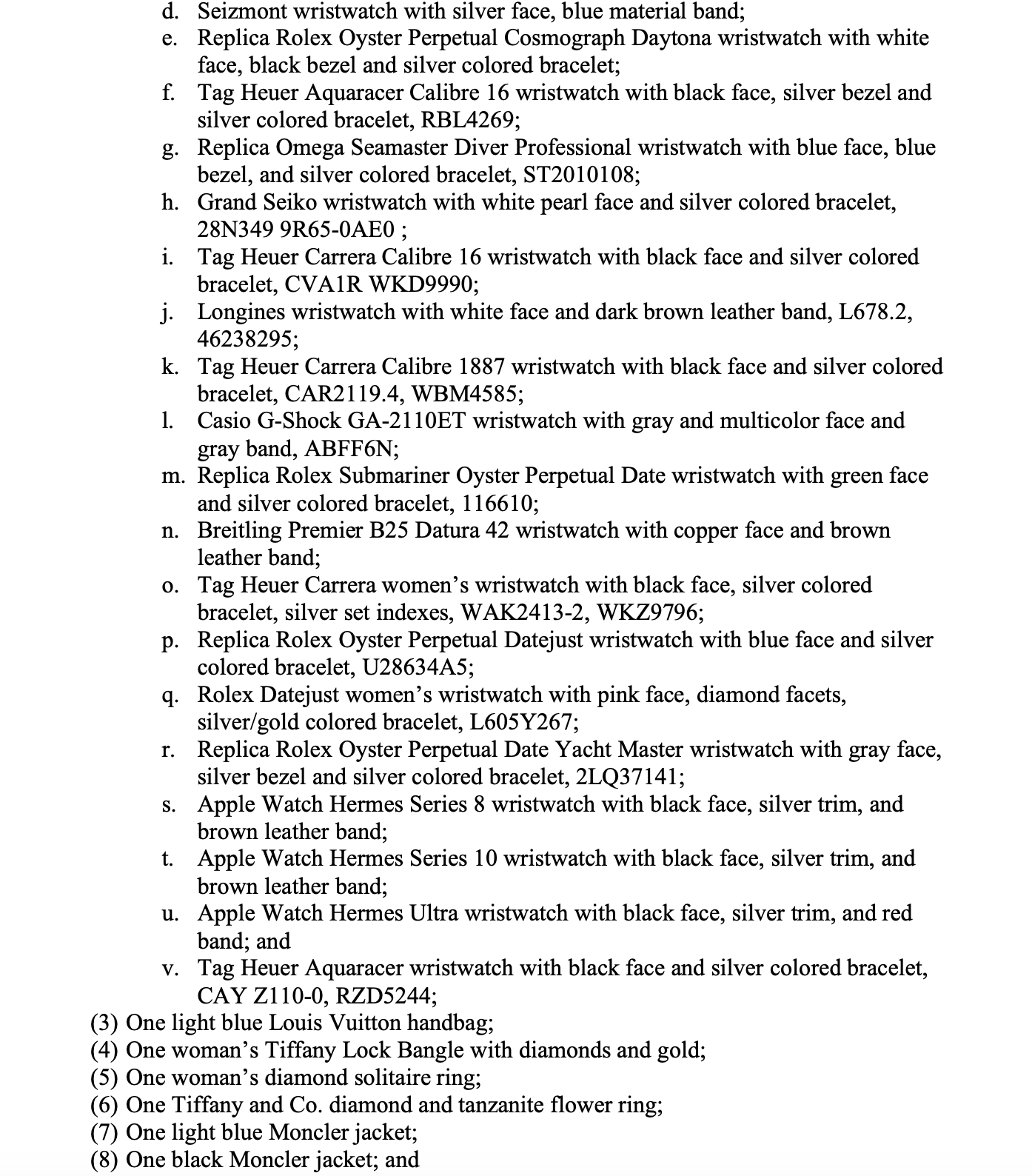
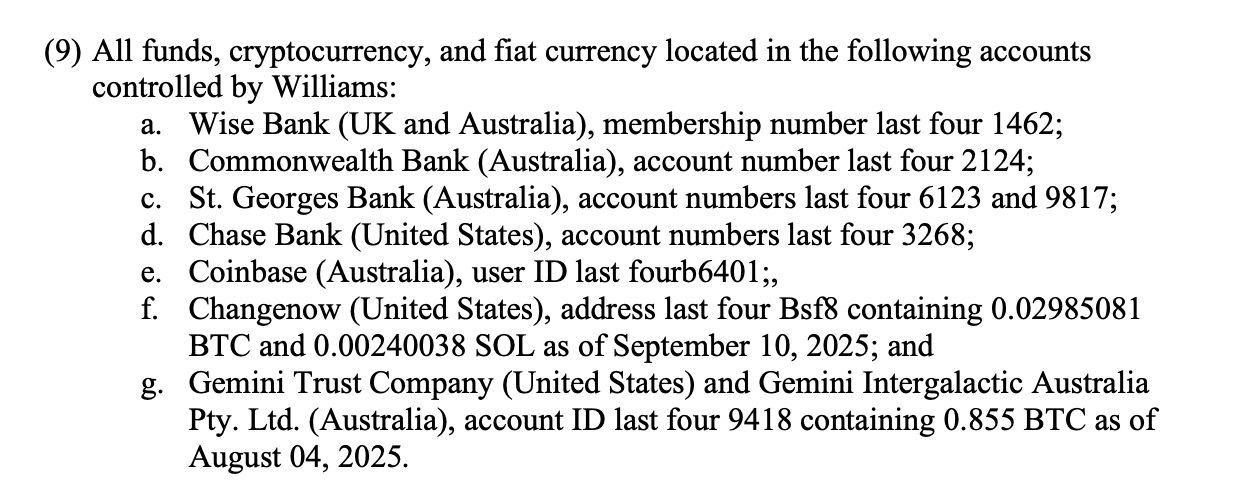
The lengthy list of property that Williams agreed to forfeit to the government under his plea agreement. It includes nearly two dozen watches -- both expensive luxury watches as well as a number of replicas of luxury watches.
Selling Spree Begins
It was in April 2022 that Williams first reached out to the Russian buyer to begin selling Trenchant exploits. Neither he nor prosecutors identify whether there was a triggering event that caused him to choose that particular moment to move from a lifetime of service to country, community and company to his new double life.
It's also not clear if Williams had already begun to download code from Trenchant's servers before he reached out to the buyer, but he created an email account under the pseudonym John Taylor with a company that provides anonymous and encrypted email services and contacted Operation Zero to begin his years-long relationship with the Russian broker. Prosecutors say he ignored the national security implications and chose to sell to Operation Zero simply because the Russian broker paid the highest rate for exploits on the open market.
Prosecutors have never identified the exact nature of the tools that Williams sold – for example, whether they were exploits for hacking iPhones, Android phones or browser software. They only refer to the stolen tools as Items 1-8, and note that Trenchant sold its products both as multi-functional tools with a number of components included, or as individual and subsets of components.
During his first interaction with Operation Zero, Williams negotiated a $240,000 price for "Item 1" to be paid in cryptocurrency, with additional payments to come once the Russian firm confirmed the exploit worked. Williams was also contracted to receive additional payments for any updates he provided for the tool – for example, if the maker of the software the exploit targeted released a patch to fix the vulnerability the exploit targeted and Williams provided an updated exploit capable of bypassing that fix.
Williams negotiated agreements for each of the 8 tools he sold the buyer - each provided him with an upfront payment, followed by a promise of additional payments for updates or follow-on support he provided after the sale. In total, the contracts promised Williams more than $4 million; of this, he received upfront payments in excess of $1.2 million, prosecutors say.
In September 2023, two months after Williams moved to the US to begin working out of Trenchant's DC offices, Operation Zero posted a message online announcing it was increasing its purchase prices for some mobile phone exploits to between $200,000 and $20 million. Two months later, Williams finalized an agreement to sell "Item 2" for $2 million.
Things were also going well for him on the job front. In October 2024, Williams was appointed director, or general manager, of Trenchant. But that same month, the FBI alerted Trenchant that some of its products or code had fallen into the hands of a foreign zero-day broker.
Trenchant initiated an internal review, with Williams overseeing the person conducting the investigation, and confirmed that an unauthorized vendor outside the US was selling one of its tools. In November, Trenchant and L3 Harris met with the FBI, and the federal agency began its own independent investigation into the theft.
Three months later, as Tech Crunch has previously reported, a Trenchant developer was called into Trenchant's London office for what he thought was going to be a team-building exercise. Instead, when he arrived, he was ushered into a meeting room for a video call with Williams. Williams told the developer that the company suspected he was moonlighting for another firm and that he was being suspended while Trenchant conducted an internal investigation. The company then seized his electronics, including his work phone.
The developer was later fired, though he says Williams never gave a reason for his dismissal. The employee learned only from other colleagues that the company suspected he had been stealing zero-day exploits from it – exploits targeting the Chrome internet browser. This confused the developer, who denied to Tech Crunch that he had taken any tools from Trenchant, because he only worked on developing exploits for Apple iPhones and didn't have access to any Chrome exploits the company may have developed.
Following the worker's dismissal, Williams continued with his criminal activity. In June 2025, while the FBI was conducting its own investigation of the thefts, Williams signed another agreement with the Russian buyer to sell Item 8 for $500,000. Per the agreement, Williams would receive $300,000 that month, and two additional payments of $100,000 each in subsequent months, with the final payment arriving in September. He transmitted the stolen code to his Russian buyer just days before he met with federal agents to discuss their investigation.
On July 2, Williams met voluntarily with FBI agents for an interview, during which he told the agents what he believed was the most probable way for someone to steal code from Trenchant's air-gapped secure network without triggering internal detection systems. "Air-gapped" means the network was not connected to the internet and therefore could not be accessed remotely by hackers. Williams explained that someone with access to that secure network – an insider, for example – could download material from that network onto a mobile phone or external drive. Williams had “super user” access to Trenchant’s secure network — meaning he could view all activity, logs, and data on the network, including the company's hacking tools – so he fit the description of an insider who had the ability to pull this off. Later, when Williams was caught, he acknowledged to agents that the scenario he had described to them during their June meeting was exactly how he had siphoned the code from Trenchant's network.
He also told the agents that he believed the estimated value of just Items 1 and 3 of the stolen material was about $35 million – meaning this was potentially the amount of the revenue that Trenchant lost from their theft. Prosecutors would later use this against him by demanding the court set his restitution payments at $35 million.
On August 6, while Williams was awaiting additional payment from his Russian buyer for Item 8, he had a second voluntary interview with FBI agents at the Trenchant offices in DC. Agents had already gathered sufficient evidence against Williams and had obtained a search warrant for his home, which other agents were about to execute.
In the meantime, the agents meeting with Williams asked him what he knew about Operation Zero and if he had any additional information about the theft of Trenchant's tools that might be helpful to their investigation. Williams continued to play dumb. Then about an hour into the interview, the agents suddenly changed their tone and confronted Williams with evidence that he had committed the crimes. This included receipts for the cryptocurrency payments he had received from the buyer, copies of the contractual agreements he had made with the buyer, and evidence of his use of anonymized email accounts to communicate with the buyer.
Williams dropped the pretense and admitted to his crimes. He was fired from Trenchant that same day, though documents show he formally resigned from his position as director of Trenchant on August 21st. On October 10, while the public was still unaware of what had occurred, he signed a plea agreement.

On October 21, the first hint of what occurred at Trenchant – though certainly not the whole story – became public when Tech Crunch published a story about the Trenchant developer who had lost his job as a result of a company investigation into stolen tools. Williams was mentioned in the story only because he had been on the surprise Zoom call with the developer when arrived to the company's UK office expecting a team-building exercise. Two days after the Tech Crunch story published, the Justice Department announced that Williams had been charged with theft of eight trade secrets from an unnamed firm and had sold them to an unnamed buyer in Russia. The announcement provided little detail, but the Tech Crunch story published days earlier made it clear the company was Trenchant.
At Williams' first public court hearing on October 29 in DC, reporters in attendance (including myself) expected Williams to plead not guilty. Instead, it quickly became clear that Williams had already signed a plea agreement. Williams sat silently in the courtroom, except when the judge asked him to confirm his guilty plea. In February this year, Williams was sentenced to 78 months in prison.
Williams remains out of prison until his restitution is determined by the court, at which point the court should set a date for him to voluntary surrender himself to begin his sentence. His restitution hearing is scheduled for late May, though prosecutors have asked – and the court has granted – to have the hearing closed to the media and public. They did this so that Trenchant and representatives of the intelligence community can freely discuss with the judge the sealed impact statements they submitted to the court describing the nature of the tools Williams sold to the Russian buyer and the harms that the sale of the code has caused.
In the meantime, Williams' attorney told the court that his client begun receiving treatment for anxiety and depression.
Aftermath
Williams' conviction has "forever changed the trajectory of an otherwise exemplary personal and professional life," his attorney noted recently in court documents. "He has permanently lost the career he spent decades building, along with his professional reputation and standing in the community." These are losses that "are not speculative, nor will they fade with the passage of time."
His wife and children have lost their home in DC – which was sold in January before Williams' sentencing – and have had to move back to Australia, according to court documents, making it unlikely they will see their father much until his release from prison in seven years. Williams may try to petition the court to serve his sentence in Australia, but prosecutors didn't appear to be amenable to this in court documents filed earlier this year. His attorneys didn't respond to questions asking if they would be seeking this. If he serves his sentence in the US, he will be deported to Australia once he has completed it.
"The impact on Peter and his immediate family has been profound," according to his brother, who told the court that he and his parents have been providing financial and moral support for his brother and his family while he awaited sentencing – which included covering his living accommodations and expenses in the US, therapy costs (which he began in August after admitting his crimes), and help with re-locating his family back to Australia.
Since news of his crimes became public, his attorney says that Williams has "endured relentless public condemnation," both in the US and Australia.
"He has been abandoned by friends, shunned by colleagues, and subjected to intense public humiliation and disgrace." In addition to this, both of his parents are entering their elderly years and living far away in Australia, his attorney wrote the court.
"Mr. Williams knows he may never see them again."
If you find this article valuable, you can leave a one-time tip to express appreciation to the author.
See Also:
Trenchant Exec Who Sold Employer's Zero-Day Exploits to Russian Buyer Sentenced to 7 Years in Prison
US Government Disclosed 39 Zero-Day Vulnerabilities in 2023, Per First-Ever Report
How to Contact Me
If you have information about Peter Williams, Trenchant or his sale of exploits to Russia -- or information about similar activity by others -- you can contact me securely on Signal at KimZ.42 or via email to: kzetter@protonmail.com. Use a non-work device or email address to reach out.
If you'd like to advertise on Zero Day, you can reach me at countdowntozeroday@gmail.com.