How North Korean Workers Tricked U.S. Companies into Hiring Them and Secretly Funneled Their Earnings into Weapons Programs
Thousands of IT workers allegedly working on behalf of North Korea managed to trick U.S. companies into hiring them as remote developers — then used the money to help finance North Korean weapons.
The methods they employed to hide their identities were extensive. They used fake web profiles and stolen identification documents and Social Security numbers; they paid U.S.-based workers to conduct video job interviews and web-conferencing calls on their behalf; they even convinced American workers to let them tunnel in through their laptops, WiFi networks and IP addresses to conceal their true location from the U.S. companies that hired them.
This is how remote IT workers connected to North Korea allegedly hid their identities from companies in the U.S. and elsewhere who hired them for coding and development work; and it’s how they earned millions of dollars, which they allegedly funneled back to North Korea to bypass sanctions and fund the country’s ballistic missile program.
On Wednesday the Justice Department announced that “thousands” of IT workers connected to North Korea were unwittingly hired over several years by unnamed customers in the U.S. and elsewhere. North Korea sent the workers to live in China and Russia to conceal their connection to the country. There they worked for two companies — Yanbian Silverstar Network Technology in China, and Volasys Silver Star in Russia — that allegedly helped coordinate the deceptive work-for-hire operations to fill North Korea’s coffers. In some cases, the FBI says, the remote workers also gained access to the networks of the U.S. companies that hired them, and stole information from them.
The court records don’t indicate when the schemes began, but in 2018, the Department of Treasury’s Office of Foreign Asset Control put Yanbian Silverstar and Volasys Silver Star on a sanctions list, along with a North Korean national named Jong Song Hwa, whom the U.S. said was CEO of the two companies.
All were sanctioned for channeling “illicit revenue to North Korea from overseas information technology workers disguising their true identities and hiding behind front companies, aliases, and third-party nationals.” According to a Treasury Department statement at the time, the companies used pseudonymous email and social media accounts to create fake identities for the North Koreans IT workers, then advertised their services on online marketplaces designed for contract workers.
In May 2022, the State Department, Department of the Treasury, and the FBI issued an advisory warning that North Korean actors were concealing their identities to obtain remote employment in the U.S. But by then, the scheme had been operating already for years.
The operation was so prolific that Jay Greenberg, special agent in charge of the St. Louis FBI office, told reporters this week that any company that hired freelance IT workers over the last few years “more than likely” hired someone involved in the operation.
The FBI field office in St. Louis, Missouri, managed recently to seize about $1.5 million in funds obtained through the deception, as well as 17 web domains that were used to market some of the workers, but warned that the North Korean activity is still ongoing.
How It Works
According to the FBI, the operators use various methods to conceal the identity of the workers. They buy, steal or counterfeit identity documents that they use to apply for remote freelance work through online job portals, or they pay individuals to pose as them for online interviews and video-conferences — the individuals may or may not know they are sitting in for North Korean workers, the FBI says.
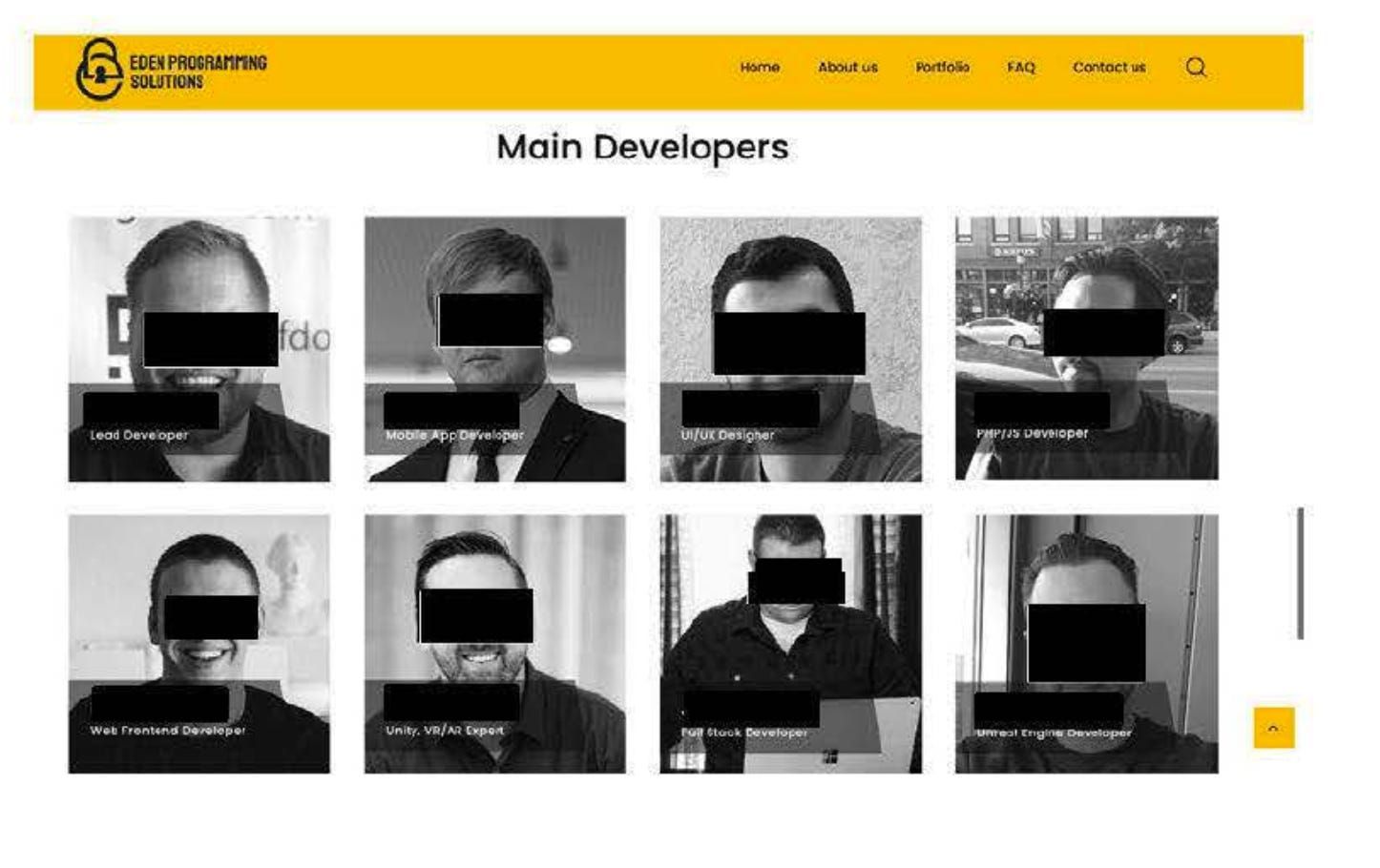
Some of the North Korean workers use VPNs to hide their location and register on job platforms for contract workers. Or they create web sites for fake app and web site development companies — companies purporting to be based in the U.S. — and will even hire developers to build a portfolio of work for them, giving them an air of legitimacy, the FBI says in an affidavit. These company web sites feature photos of non-North Korean individuals, leaving employers in the dark about who they are really hiring.
Court documents (you can find four of them linked at the bottom of this page) identify a number of these shell companies purportedly based in the U.S. and China that hire out the North Korean workers. They include Eden Programming Solutions (purportedly based in Fremont, California); Foxy Sun Studios (which lists an address in San Francisco that the FBI says doesn’t exist); BabyBox Technology (the web site indicates it’s in California; the domain registration lists a Georgia address); and Silver Star China (based in Jilin, China). The FBI says the web sites are all front operations used by Yanbian Silverstar to hire out North Korean IT workers.
The FBI gained access to email and slack accounts where it says North Korean workers discussed the illicit operations; the bureau also ran undercover operations to entice North Korean workers to communicate with people working for the FBI and reveal their schemes.
One investigation began in August 2019 when a freelance IT worker based in the U.S. contacted the FBI with a tip. The worker maintained an account on a global freelancing platform used to market professional services. The individual revealed that he had allowed someone overseas to use his freelance account to obtain work, and had purchased four inexpensive laptops that the overseas operator used to do work for clients in the U.S. The laptops had remote-desktop software installed on them so the overseas worker could use and control them remotely as if he were sitting at the keyboards. And because they used U.S. IP addresses, the overseas worker could appear to be in the U.S. whenever he signed in to a client’s network.
The U.S. individual revealed that he received $400 a month for the proxy laptops that he set up for the overseas operator to use; he also received an unspecified percentage of income the operator earned for the freelance IT work (likely 15 percent). Clients sent the money to the U.S. individual’s account, who then sent it to a China-based bank account, minus the fee. Between April 2018 and October 2019 the overseas operator earned $85,000 from this freelance work. The FBI tracked the email address the person used and other information to determine that the individual was actually a North Korean IT worker living in China and working for Yanbian Silverstar.
The FBI doesn’t reveal in court documents exactly how much money has been funneled to North Korea’s weapons programs in this way, but says millions of dollars have been involved.